Active Directory Account Lockout Policy | Win Server 2025
Best Practices to Setup Password and Account Lockout Policies

Table of Contents
Configuring Active Directory Account Lockout Policy in Server 2025
Active directory account lockout policy plays a vital role in user account security.
As you already know, nowadays there are different types of attacks hampering business productivity.
It is very important to consider the Password and Account lockout policy in the Active Directory environment.
By properly configuring password and Account lockout policies, you can prevent unauthorized users from logging into your network.
Therefore, in this article, we will learn how to set Account lockout policy in an Active directory running on Windows Server 2025
What is an Account Lockout Policy?
It’s an important policy available on all versions of Windows servers, that decide when to lock the account and for how long it should be locked.
Whenever policy determines the unauthorized access to the account.
It may lock the account for the duration defined by the administrator.
However, it can prevent password guessing, brute force attacks, etc.
This policy can be implemented via group policy to apply to particular OUs in the organization or to the complete domain as well.
Every Administrator must configure this Account lockout policy to secure their user’s account.
How to Set Account Lockout Policy
It is a good idea to implement the policy as a default domain policy to apply to the entire domain.
To configure the Account lockout policy Open the Server Manager
Go to the tools and click on Group Policy Management.
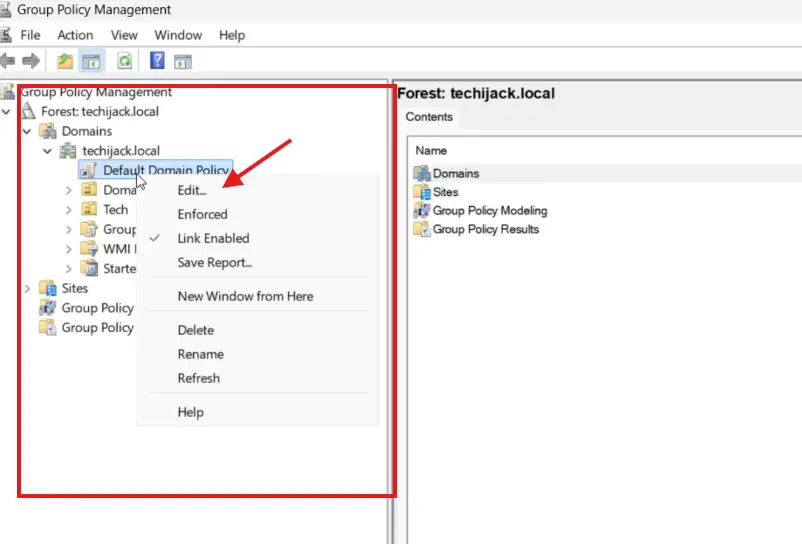
So, once the group policy management is open, expand the forest, Domains, and your domain
Under your domain, you will see the Default Domain Policy
Just right-click the policy and click on Edit.
After clicking on the edit button.
The group policy management editor will get an open
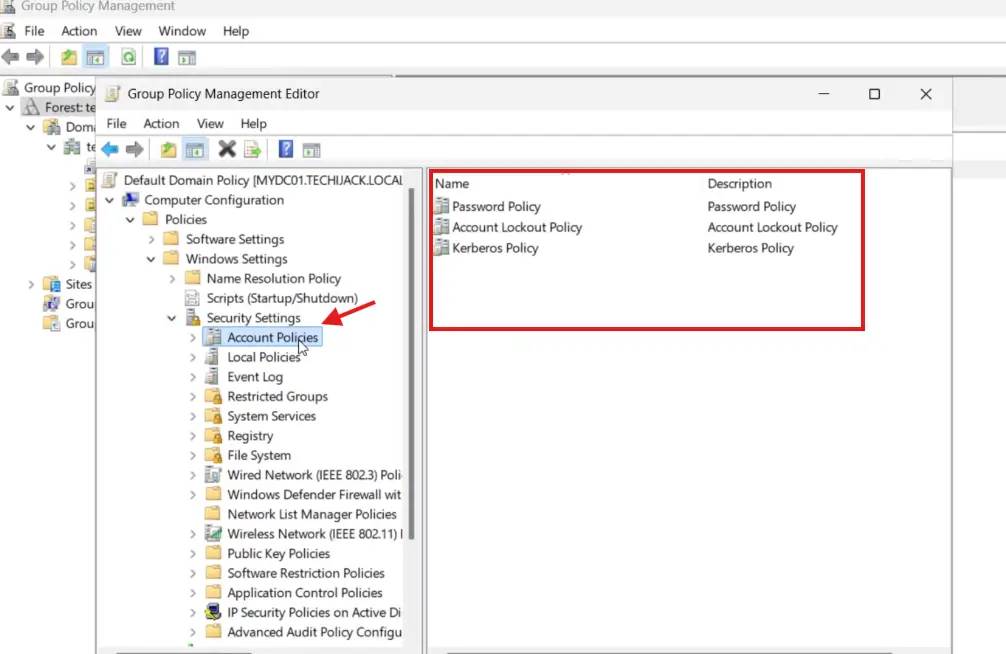
Now under the computer configuration expand the Policies – Windows Settings – Security Settings
Under the security settings, you will see the account policies
Therefore, you will see three policies inside the account policies
Password Policy – Account Lockout Policy and Kerberos Policy
Inside the Account Lockout Policy, we have four settings in Windows Server 2025
- Account lockout duration
- Account lockout threshold
- Allow Administrator account lockout
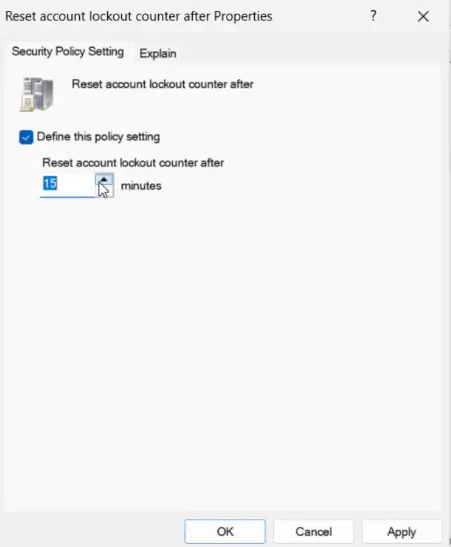
- Reset account lockout counter after
- Majorly we work with three main settings
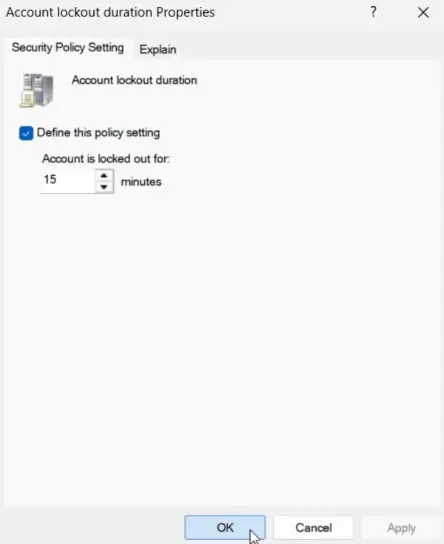
Account lockout duration: It’s a duration of minutes the account will be locked out before it gets automatically unlocked. (By default it is not defined)
You can set it to 15 minutes as shown in the image below
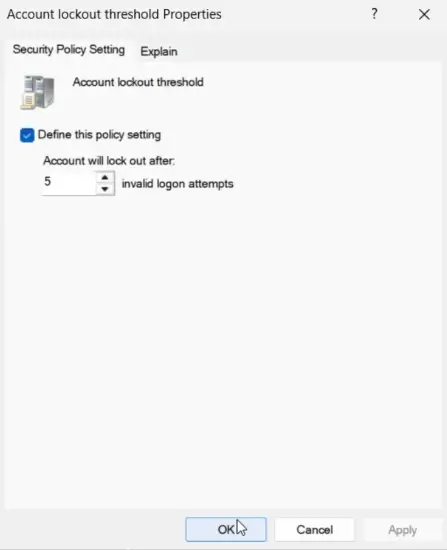
Account lockout threshold: This defines that, how many failed login attempts are allowed before the account gets locked out.
You can choose the value 5 as the default value it is also 5.
Allow administrator account lockout: Make sure to keep this enabled. (By default it is enabled)
Reset account lockout counter after: This will reset the locked account after the lockout duration has passed.
Keep this setting to 15 minutes. (By default it is 10 minutes)
Updating Group Policy
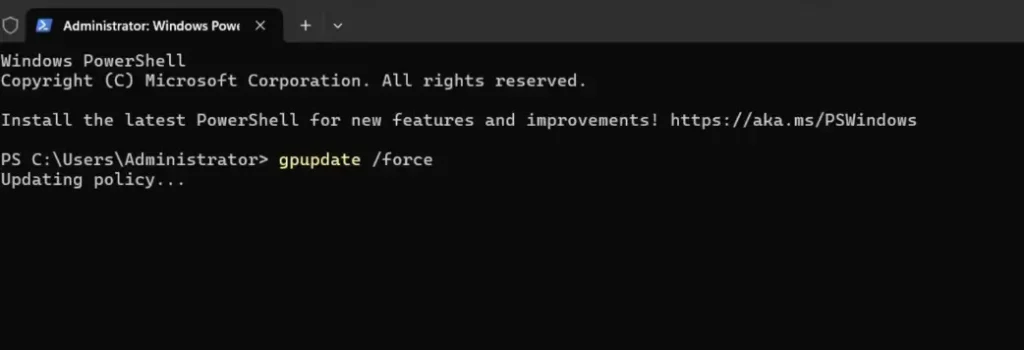
Once you do all the above steps.
Update the group policy setting on your server and client machine by running the gpupdate /force command.
Now if you try to test any Active Directory user account by typing an invalid password.
Therefore, the user account will be locked.
In our case, we tried to type the 5 invalid passwords and now the user is locked and giving the message as below image.
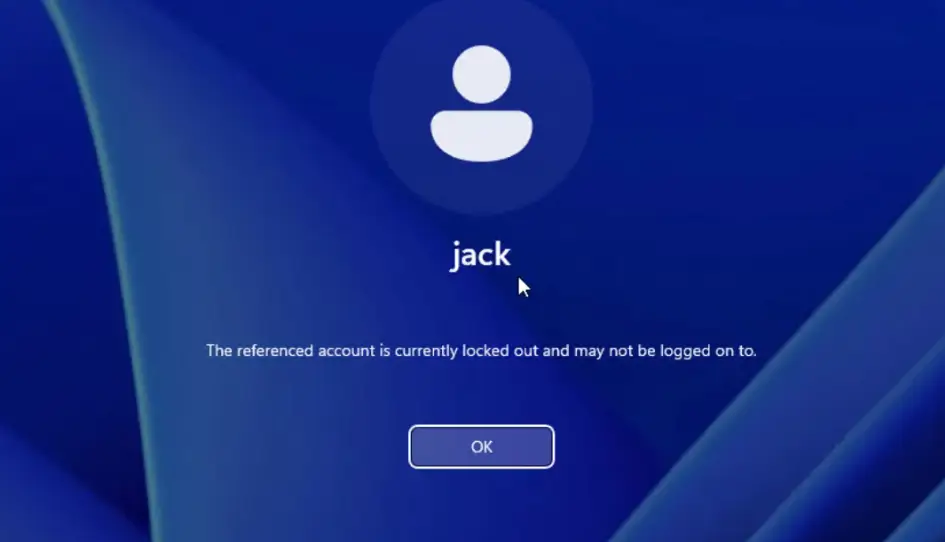
Now our user is locked out.
So, it means that our Active Directory Account lockout policy is working perfectly fine.
How to unlock the User Account in Active Directory
Now the user Jack is locked out by the Account lockout policy.
Here we did it intentionally, so to unlock the user
Go to the Active Directory Users and Computers, go to the locked user, and right click the user, and click on properties
Now go to the Account tab and you will see the user is locked, along with a locked message
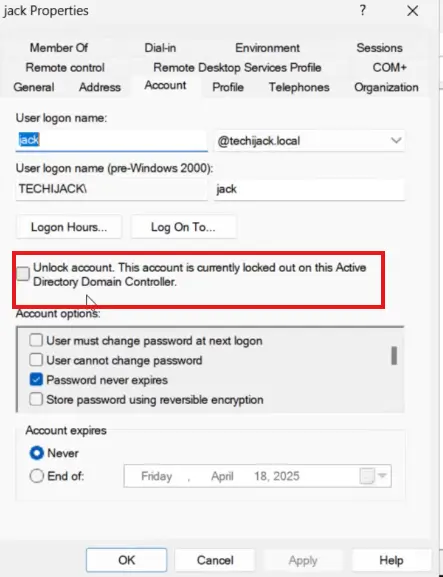
To unlock the user, you just need to check the box and click on apply.
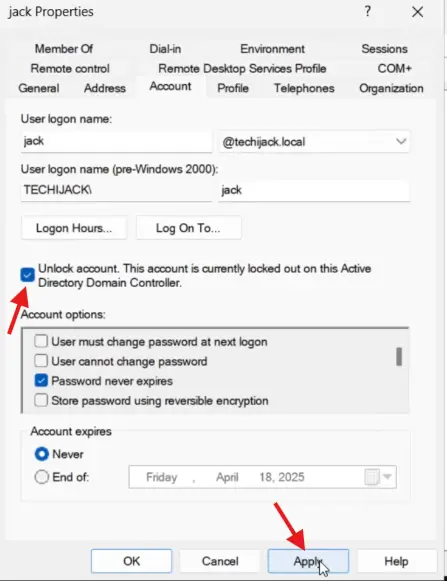
Once you do that, now the user will be unlocked and will be able to log in again with the correct password.
Conclusion
Whenever working with Active Directory, make sure to follow best practices to configure the password and account lockout policy to prevent users from brute force attacks, password guessing, etc.
So, it can be very beneficial for the security purpose of the user and can prevent much damage.
Finally, we learned how to configure the Account lockout policy, and how to unlock the user account if it is locked.
In case of any issues related to this post, feel free to contact.
However, you may also like some other posts on Active Directory
Furthermore, if you want to see the step-by-step guide to set up the password Policy and Account lockout policy in the Active Directory environment. Watch the video below.



