Azure Active Directory & Its Benefits | 5 Imp Points to Know
AD DS Vs Azure Active Directory Domain Services
Table of Contents
What is Azure Active Directory Domain Services
Azure active directory Domain Services is identity management and cloud-based directory service.
It gives an easy solution of (SSO) single sign-on to employees and business partners.
Therefore, by the help of SSO, you can access your cloud applications like office 365, dropbox, etc.
The azure active directory helps developers to focus on the application by making them fast and easy to integrate.
So, with Azure AD, you have access to a set of features that aren’t available in Active Directory Domain Service.
For Example Multifactor authentication, identity protection, and self-service password reset.
However, you can use Azure AD to provide more secure access to cloud-based resources for organizations and
individuals by:
- Configuring access to applications.
- Configuring single sign-on (SSO) to cloud-based software-as-a-service (SaaS) applications.
Managing users and groups. - Provisioning users.
- Enabling federation between organizations.
- Providing an identity management solution.
- Identifying irregular sign-in activity.
- Configuring multifactor authentication.
- Extending existing on-premises Active Directory implementations to Azure AD.
- Configuring Application Proxy for cloud and local applications.
- Configuring conditional access for users and devices.
Moreover, all the new subscriptions include the basic azure service as a free tier.
Azure Active Directory Domain Services Benefits & Features
The azure ad provides the secure single sign on to on-premises and cloud application
Such as Office 365, box, DocuSign, and thousand of SaaS applications.
Users can launch applications from a private web-based access panel, mobile app, Office 365.
Therefore, users can also launch the app from custom company portals using their existing work credentials.
All users have the same experience as they are working on Mac, IOs, Android, or Windows devices.
A user can access on-premises web application form anywhere with multi-factor authentication.
Additionally, group bases access management and conditional access policies protect the data.
It provides an easy connection with on-premises AD and Azure AD in a few clicks.
Azure Ad maintains a consistent set of users, groups, passwords, and devices across both environments.
It protects suspicious sign-in activities and potential vulnerabilities.
Therefore, it also provides unique identity protection to enhance application security.
Moreover, it protects the business from current and future threats.
Provides self-service application access and password management through verification steps.
Delegates the task such as password resetting and creation and management of groups.
If you are already using a service like an office 365 that means you are using AD tenant.
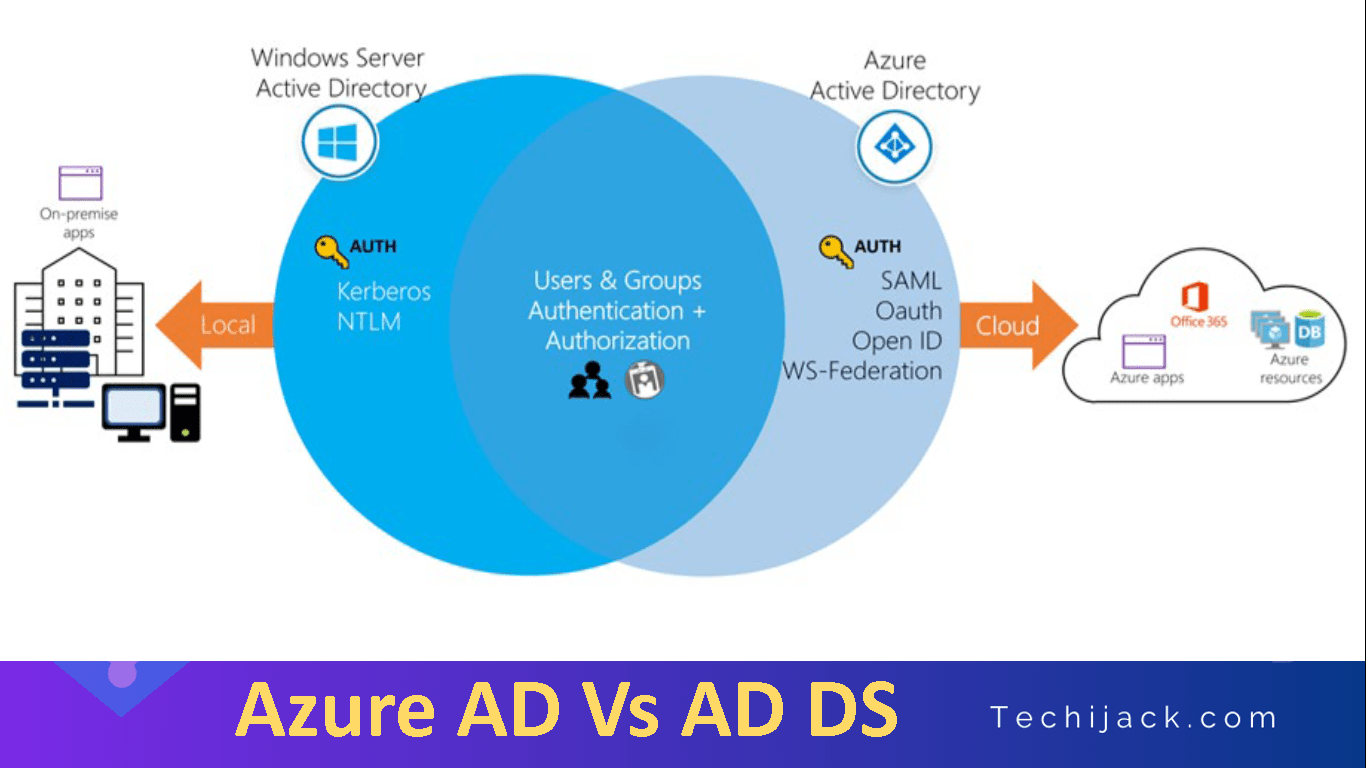
AD DS vs Azure Active Directory
Though AD DS and Azure AD has many similarities, there are also many differences.
Deploying an AD DS on an Azure virtual machine is totally different from using Azure AD.
Let’s see the difference of Azure AD Below
Identity Solution:
Azure AD is an identity solution.
Therefore, it is designed for Internet-based applications by using HTTP and HTTPS communications.
REST API Querying:
Because Azure AD is HTTP/HTTPS based, it cannot be queried through LDAP.
Rather than using the LDAP, Rest API over HTTP & HTTPS are used by Azure Ad.
Communication Protocols:
Azure AD is HTTP/HTTPS based, it does not use Kerberos authentication.
However, it uses HTTP and HTTPS protocols such as SAML, WS-Federation, and OpenID Connect for authentication
Federation Services:
Azure AD includes federation services, and many third-party services (such as Facebook).
The Flat Structure of Azure Active Directory Domain Services:
Azure AD users and groups are created in a flat structure, and there are no Organizational Units (OUs) or Group Policy Objects (GPOs).
An Admin can only manage users, groups, and policies in Azure AD.
However, if you are Deploying Active directory service VMs on Azure.
That means you have to manage all deployment tasks, configuration, patching, etc.

Characteristics Of AD DS
Active directory domain services are known as primary directory services.
ADDS is a suite of technologies, which includes AD Certificate services, AD LDS, AD FS, and AD RMS
Furthermore, when comparing AD DS with Azure AD, it’s important to note the following characteristics of AD DS:
- Active Directory Service is a true directory service, with a hierarchical based structure.
- AD DS uses a Domain Name System (DNS) for locating resources such as domain controllers.
- You can query and manage AD DS by using Lightweight Directory Access Protocol (LDAP) calls.
- primarily uses the Kerberos protocol for authentication.
- AD DS uses organizational units (OUs) and Group Policy Objects (GPOs) for management.
- It includes computer objects, representing computers that join an Active Directory domain.
- Uses trust between domains for delegated management.
Note: However, deploying AD DS on an Azure virtual machine does not make any use of Azure AD.
Azure AD Authentication Protocols
Azure Active Directory authentication protocols differ from AD DS authentication protocols.
Often, AD DS administrators are less experienced with web-based authentication protocols.
In addition to Azure AD, authentication protocols are quite different from ADDS
- OAuth 2.0. Based on RFC 6749, is an open standard for authorization that provides precise access control to destination services.
- SAML 2.0. is an open standard XML protocol that consists of security tokens.
- A security mechanism of WS-Federation allows identity federation so that users on one side, or directory, can access resources of another side.
Learn More